Whilst web server and the like are a primary target there also has been spearphishing attacks on companies. This spearphishing has taken the form of:
- links to credential harvesting websites
- emails with links to malicious files, or with the malicious file directly attached
- links prompting users to grant Office 365 OAuth tokens to the actor
- use of email tracking services to identify the email opening and lure click-through events.
Once initial access is achieved, the actor utilised a mixture of open source and custom tools to persist on, and interact with, the victim network. Although tools are placed on the network, the actor migrates to legitimate remote accesses using stolen credentials. To successfully respond to a related compromise, all accesses must be identified and removed.
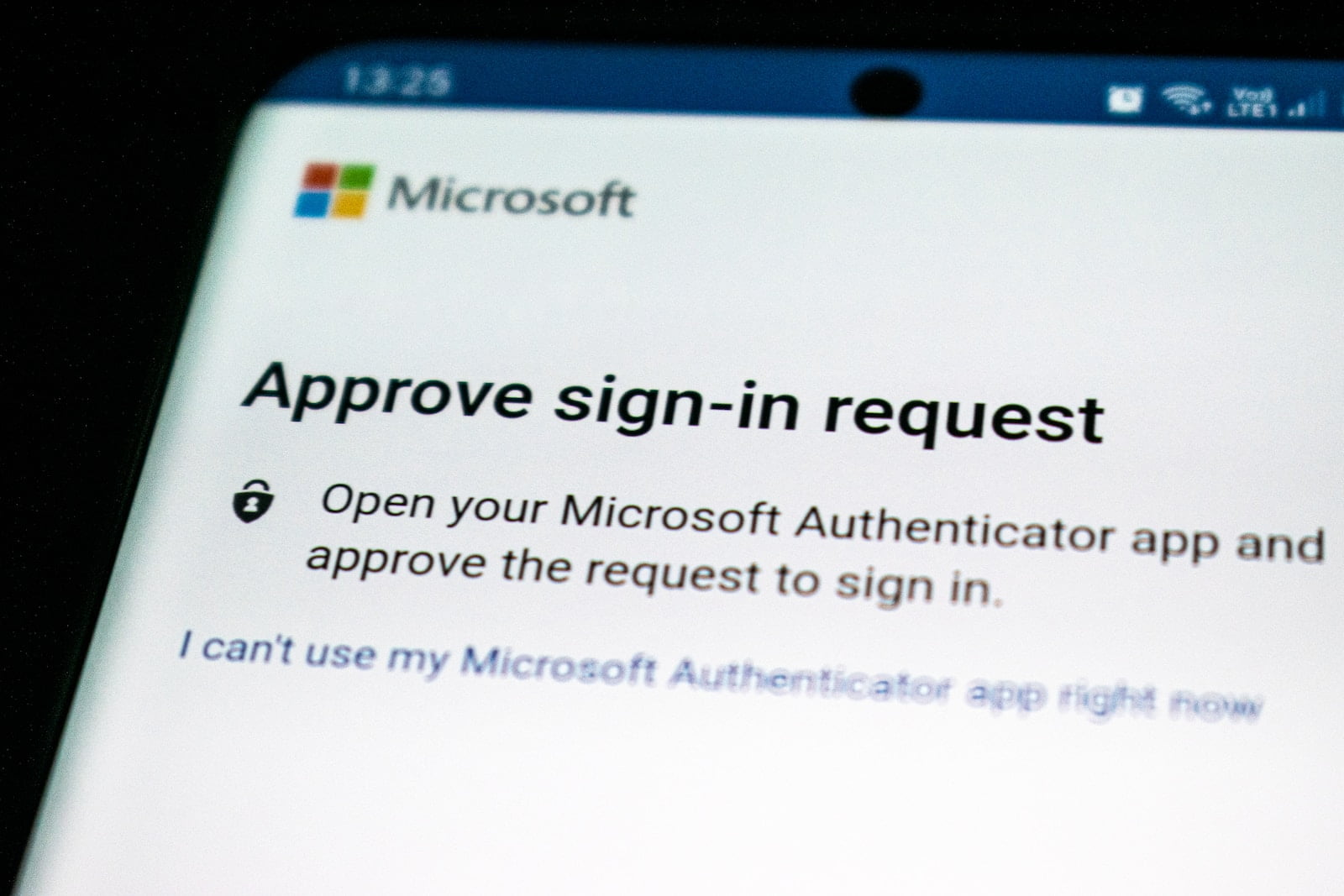
Now is a good time to ensure that all your company email accounts have Two Factor Authentication enabled. In the event that you accidentally click on a suspicious link and then enter in your username and password, the secondary authentication will reduce the likelihood of the attacker gaining access to your email account.
More information can be found on the ACSC website